At ClayHR we take comprehensive measures to protect our infrastructure, network, and applications; train employees in security and privacy practices; build a culture where being worthy of trust is the highest priority, and put our systems and practices through rigorous testing and auditing.
While ClayHR is responsible for securing each aspect of the service that’s under our control, customers play a key role in ensuring their teams and data are protected and secure. If you are a site admin of your ClayHR cloud site, you have the ability to configure, use, and monitor your account in ways that meet your organization’s security, privacy, and compliance needs.
We’ve put together this guide to help you understand what ClayHR does to keep your account safe, and what you can do to maintain visibility and control over your team’s data. At a high level, ClayHR handles the security of the application, the system it runs on, and the environment the system is hosted within.
ClayHR Responsibility
Encrypt user data
ClayHR customers interact with our systems through our mobile, desktop, and web applications, and APIs. Regardless of which app you’re using, we protect your data both in transit and at rest.
Data in transit
To protect data in transit between ClayHR apps and our servers, ClayHR uses Secure Sockets Layer (SSL)/Transport Layer Security (TLS) for data transfer, creating a secure tunnel protected by 128-bit or higher Advanced Encryption Standard (AES) encryption. File data in transit between a ClayHR client (currently desktop, mobile, API, or web) and the hosted service is encrypted via SSL/TLS.
For endpoints we control (desktop and mobile) and modern browsers, we use strong ciphers and support perfect forward secrecy and certificate pinning. Additionally, on the web we flag all authentication cookies as secure and enable HTTP Strict Transport Security (HSTS) with include SubDomains enabled. To prevent man-in-the-middle attacks, authentication of ClayHR front-end servers is performed through public certificates held by the client. An encrypted connection is negotiated before the transfer of any files ensures secure delivery to ClayHR front-end servers.
Data at rest
ClayHR files at rest are encrypted using 256-bit Advanced Encryption Standard (AES). Files are stored in multiple data centers in discrete file blocks. Each block is fragmented and encrypted using a strong cipher. Only blocks that have been modified between revisions are synchronized.
Customer Responsibility
Configure sharing and viewing permissions
ClayHR gives you the flexibility to configure your account to support your security, collaboration, and privacy needs. Admins can review and modify these settings through the Admin Console to reflect their sharing or regulatory environment.
Team members
Team members can be easily added, removed, and reviewed from the Admin Console. To ensure sensitive data in your ClayHR account can only be accessed by the right people, we recommend frequently reviewing this list. You can then remove access when someone leaves your organization or no longer requires access due to a change in job role. Similarly, you can modify team members’ roles in the Admin Console so that each user account has the appropriate level of access.
Shared responsibility
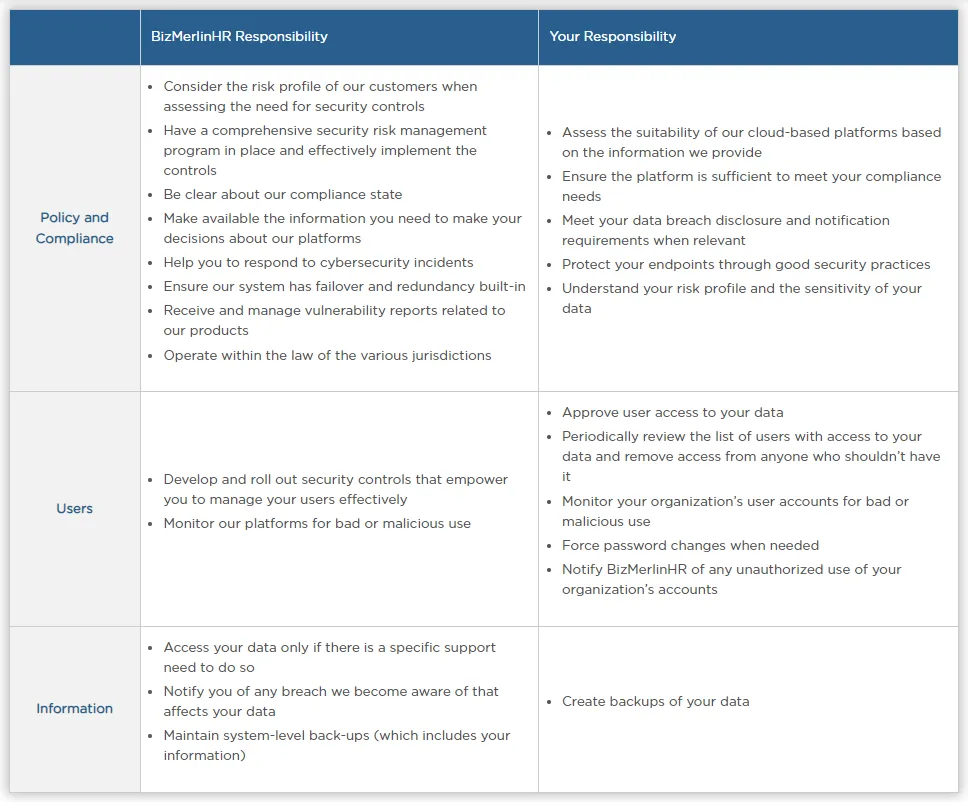
At ClayHR, we have identified three areas as shared responsibility.
- Policy and compliance: Ensuring that the system meets your business needs and is operated in accordance with industry, regulatory and legislative compliance obligations.
- Users: The creation and management of user accounts
- Information: The content that you create on ClayHR apps